PocketBook 7.8", Android 5.5": MD to HTML with MS VSC +
Markdown All in One by Yu Zhang
Google Chrome -> print to pdf -> A4, Portrait,
Margins: top, bottom .4" left, right 0", Scale 130%
[ ] Headers and Footers
[ ] Background Graphics
234567891123456789212345678931234567894123456789512345678961
--------|---------|---------|---------|---------|---------|-
May 14, 2020
http://woshub.com/manage-windows-firewall-powershell
This article gives the basics on how to manage settings and rules of built-in Windows Defender Firewall with Advanced Security using PowerShell. We’ll consider how to enable/disable the firewall for different network profiles, create or remove firewall rules and write a small PS script to get a convenient table showing the current set of active firewall rules.
You can manage Windows Firewall settings from the graphic console:
Control Panel ->
System and Security ->
Windows Defender Firewall
However, starting with Windows 8.1 (Windows Server 2012 R2) you can use the built-in NetSecurity PowerShell module to manage firewall.
Previously, the following command was used to manage Windows Firewall rules and settings: netsh advfirewall firewall
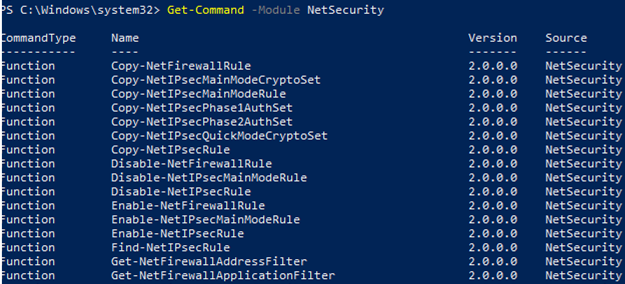
There are 85 commands available in the NetSecurity module on Windows 10. You can display the whole list:
Get-Command -Module NetSecurity
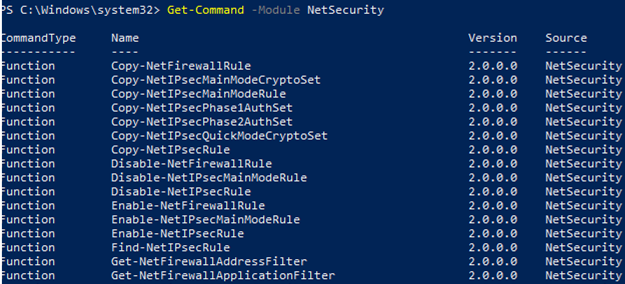
fig 1. powershell NetSecurity on windows 10 to manage windows defender advanced firewall
There are three types of network profiles in Windows Firewall:
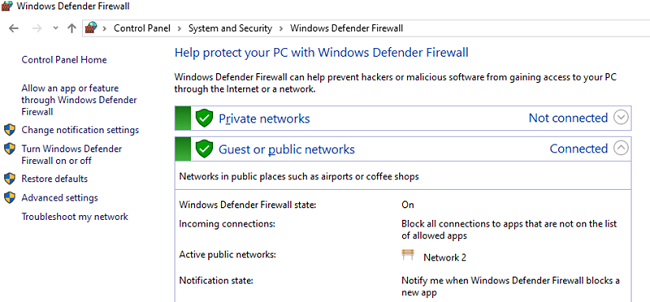
fig 2. Windows Defender Firewall network location (profiles)
Network Location Awareness (NLA) keeps the information about network types in its database. You can change your network profile (location) if it has been detected incorrectly.
Each network profile (location) may differ by the set of firewall rules used. By default, all network interfaces of a computer are protected by the firewall, and all three types of profiles are applied to them.
To enable all three network profiles: Domain, Public and Private, use this command:
Set-NetFirewallProfile -All -Enabled True
Or set the specific profile instead All:
Set-NetFirewallProfile -Profile Public -Enabled True
To disable the firewall for all three network location, use the command:
Set-NetFirewallProfile -All -Enabled False
Using the Set-NetFirewallProfile cmdlet, you can change profile options (a default action, logging, a path to and a size of a log file, notification settings, etc.).
You may know that in modern OS versions Windows Firewall is enabled for all profiles. All outbound connections are allowed and inbound ones are blocked (except allowed ones) in the profile settings.
Let’s change the default action for the Public profile to block all inbound connections.
Set-NetFirewallProfile `
–Name Public `
–DefaultInboundAction Block
You can display the current profile settings as follows:
Get-NetFirewallProfile -Name Public
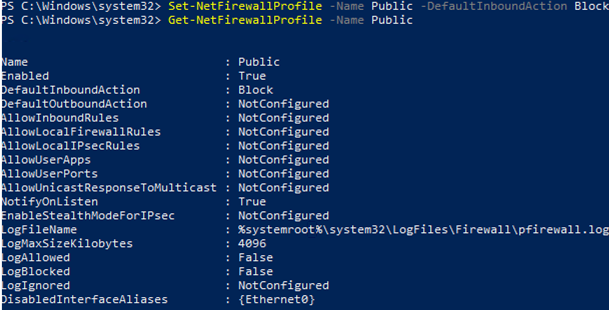
fig 3. Set-NetFirewallProfile
If you manage your Windows Firewall settings using GPO, you can display the current resulting profile settings as follows:
Get-NetFirewallProfile -policystore activestore
Make sure that all firewall settings are applied to all network interfaces of the computer.
Get-NetFirewallProfile -Name Public | `
Format-List DisabledInterfaceAliases
If all interfaces are protected, the command will return the following:
DisabledInterfaceAliases : {NotConfigured}
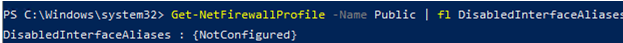
fig 4. Get-NetFirewallProfile
You can disable the specific interface profile (to display the list of interface names, use the Get-NetIPInterface):
Set-NetFirewallProfile `
-Name Public `
-DisabledInterfaceAliases "Ethernet0"`
As you can see, Public profile is no longer applied to Ethernet0:
DisabledInterfaceAliases : {Ethernet0}

fig 5. disable public location for ehernet0 interface
You can set network connection logging options at the profile level. By default, Windows Firewall logs are stored in %systemroot%\system32\LogFiles\Firewall, and the file size is 4MB. You can enable all connection logging and change the maximum file size:
Set-NetFireWallProfile `
-Profile Domain `
-LogBlocked True `
-LogMaxSize 2PSFW `
-LogFileName `
'%systemroot%\system32\LogFiles\Firewall\pfirewall.log'
There are 9 cmdlets to manage your firewall rules:
Let’s consider some simple examples of how to open ports in Windows Firewall.
For example, if you want to allow inbound TCP connections to ports 80 and 443 for Domain and Private profiles, use this command:
New-NetFirewallRule `
-DisplayName 'HTTP-Inbound' `
-Profile @('Domain', 'Private') `
-Direction Inbound `
-Action Allow `
-Protocol TCP `
-LocalPort @('80', '443')`
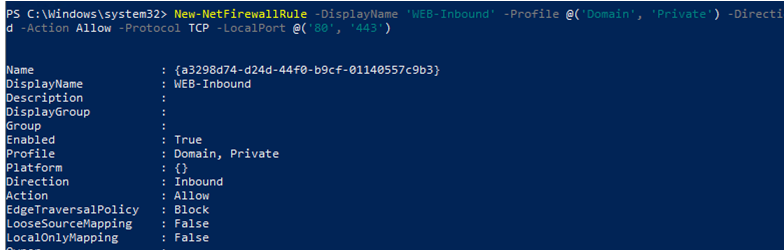
fig 6. New-NetFirewallRule create new firewall rule with powershell
You can allow or block network access for an app. For example, you want to block outbound connections for Firefox:
New-NetFirewallRule `
-Program `
"C:\Program Files (x86)\Mozilla Firefox\firefox.exe" `
-Action Block `
-Profile Domain, Private `
-DisplayName "Block Firefox browser" `
-Description "Block Firefox browser"
-Direction Outbound
To allow inbound RDP connection on port 3389 from one IP address only:
New-NetFirewallRule `
-DisplayName "AllowRDP" `
–RemoteAddress 192.168.2.200 `
-Direction Inbound `
-Protocol TCP `
–LocalPort 3389 `
-Action Allow
To allow ping (ICMP) for addresses from the specified IP subnet or IP range, use these commands:
$ips = @( `
"192.168.2.15-192.168.2.40", `
"192.168.100.15-192.168.100.200", `
"10.1.0.0/16" `
)
New-NetFirewallRule `
-DisplayName "Allow inbound ICMPv4" `
-Direction Inbound `
-Protocol ICMPv4 `
-IcmpType 8 `
-RemoteAddress $ips `
-Action Allow
New-NetFirewallRule `
-DisplayName "Allow inbound ICMPv6" `
-Direction Inbound `
-Protocol ICMPv6 `
-IcmpType 8 `
-RemoteAddress $ips `
-Action Allow
In the previous article we showed how to block site access both by IP address and by a domain/site DNS name using PowerShell.
In order to edit an existing firewall rule, the Set-NetFirewallRule cmdlet is used. For example, to allow inbound connections from the specified IP address for the rule created earlier:
Get-NetFirewallrule -DisplayName 'HTTP-Inbound' | `
Get-NetFirewallAddressFilter | `
Set-NetFirewallAddressFilter -RemoteAddress 192.168.1.10
If you want to add multiple IP addresses to a firewall rule, use this script:
$ips = @("192.168.2.15", "192.168.2.17","192.168.100.15")
Get-NetFirewallrule -DisplayName 'WEB-Inbound'|Set-NetFirewallRule -RemoteAddress $ips`
To display all IP addresses in a firewall rule:
Get-NetFirewallrule -DisplayName 'Allow inbound ICMPv4' | `
Get-NetFirewallAddressFilter
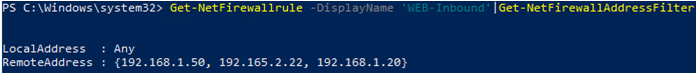
fig 7. Get-NetFirewallAddressFilter view IP adresses in firewall rule
You can enable/disable firewall rules using Disable-NetFirewallRule and Enable-NetFirewallRule cmdlets.
Disable-NetFirewallRule –DisplayName 'WEB-Inbound'
To allow ICMP (ping), run this command:
Enable-NetFirewallRule -Name FPS-ICMP4-ERQ-In
To remove a firewall rule, the Remove-NetFirewallRule cmdlet is used.
You can display the list of active firewall rules for your inbound traffic as follows:
Get-NetFirewallRule | `
where { `
($_.enabled -eq $True) -and `
($_.Direction -eq "Inbound") `
} | Format-Table`
If you want to display the list of outbound blocking rules:
```powershell
Get-NetFirewallRule `
-Action Block `
-Enabled True `
-Direction Outbound
To display an app name in a rule:
Get-NetFirewallRule `
-Action Block `
-Enabled True `
-Direction Outbound | `
%{ $_.Name; $_ | Get-NetFirewallApplicationFilter}
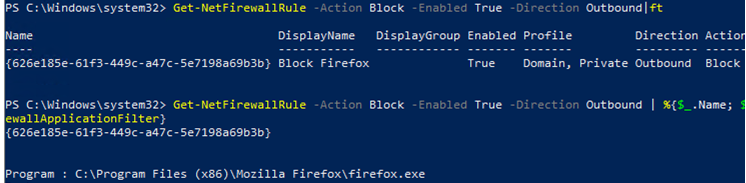
fig 8. Get-NetFirewallrule - view firewall rule properties
As you can see, the Get-NetFirewallRule cmdlet does not show network ports and IP addresses for your firewall rules. To display the detailed information about allowed inbound (outbound) connections in a more convenient way showing the port numbers, use the following PowerShell script:
Get-NetFirewallRule `
-Action Allow `
-Enabled True `
-Direction Inbound | `
Format-Table `
-Property Name, `
@{Name='Protocol'; `
Expression={($PSItem | Get-NetFirewallPortFilter).Protocol} `
}, `
@{Name='LocalPort'; `
Expression={($PSItem | Get-NetFirewallPortFilter).LocalPort} `
}, `
@{Name='RemotePort'; `
Expression= `
{($PSItem | Get-NetFirewallPortFilter).RemotePort} `
}, `
@{Name='RemoteAddress'; `
Expression= `
{($PSItem | Get-NetFirewallAddressFilter).RemoteAddress} `
}, Enabled, Profile, Direction, Action
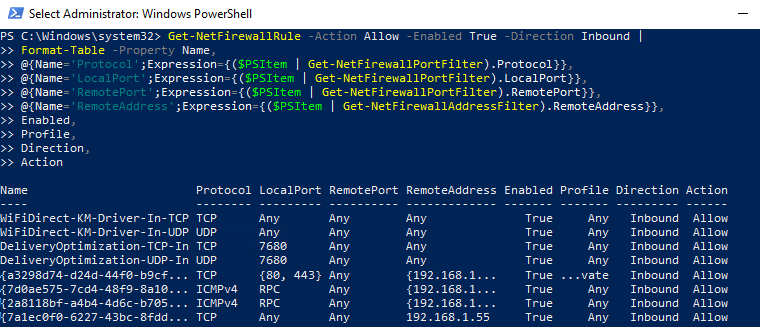
fig 9. Use PowerShell to List Firewall Rules with port numbers
PowerShell provides ample opportunities to manage Windows Firewall rules from the command prompt. You can automatically run PowerShell scripts to open/close ports if certain events happen. In the next article, we’ll consider a simple PowerShell- and Windows Firewall-based solution to automatically block IP addresses trying to remotely brute-force passwords over RDP on your Windows VDS server.